Government of Odisha launched Online Clinical Establishment Management System

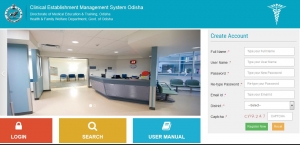
Sri Naba Kisore Das, Hon’ble Minister, Health & Family Welfare, Odisha launched the Online Clinical Establishment Management System (http://cemso.nic.in) on 7th September 2019, in presence of Dr. P.K. Meherda, IAS, Commissioner-cum-Secretary, H & FW Department.
The dignitaries present on the occasion include Dr. Dillip Kumar Sarangi, Director, Health Services, Prof. Sonamali Bag, Director, Medical Education & Training, Dr. Sushil Kumar Kar, Director, Nursing and other senior officers of the Department along with NIC officers named Dr. A. K. Hota, STD & ASIO , Ms. Nirupama Mohapatra, STD and Sri Bivas Roy, STD of NIC.
The main objective of this application is to bring transparency and resolve issues related to delay in issuance of necessary clearances for obtaining registration in the Clinical Establishment System. Nearly 1800 private hospitals and clinics will be benefited through this new system as they can able to apply and obtain No Objection Certificates (NOC) and other renewals without much hassle.
Interacting with Media Honourable Minister appreciated the effort taken by NIC to make it online.
The application developed by National Informatics Centre, Bhubaneswar under the guidance of Dr. Umakanta Satpathy, Joint Director, DMET led by technical members of NIC, Ms. Nirupama Mohapatra, STD and Sri Bivas Roy, STD is hosted in National Data Centre, Bhubaneswar. The application has been developed using Open Source Technology stack such as PHP (CakePHP Framework) and MySQL as database.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


