Honourable Chief Minister, Himachal Pradesh Inaugurates Development Schemes over VC
Ajay Singh Chahal, Himachal Pradesh
ajay[dot]chahal[at]nic[dot]in
| Oct 31, 2017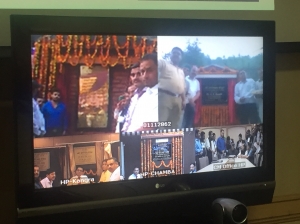

Sh. Virbhadra Singh, Hon’ble Chief Minister Himachal Pradesh on 5th October 2017 at Shimla inaugurated developmental works at various locations in district Kangra, Chamba and Shimla over the Video conferencing facility. The Video Conferencing facility set up by National Informatics Centre, Himachal Pradesh was used by the Chief Minister office and at district centre of Kangra and Chamba. Other sites were connected using Vidyo Desktop utility. The use of VC for such inaugurations and stone laying ceremonies has saved public money and time of the government functionaries.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


