Governance
Sh. Gurudas Kamat, Hon ble Min. of State for Home Affairs and Comm. and IT, Govt. of India launched Mobile Money Transfer Service on through NIC s VC
Sh. Gurudas Kamat Hon ble Minister of State for Home, Communication andIT launched Mobile Money Transfer Service of Department of Post at Chandigarh on 1st June 2011. CPMG Patna, Bihar also participated through Video Conferencing. NIC, Punjab and VC, Division NIC-Hq extended support to...
IFMS, Rajasthan Integrated Solutions for Financial Excellence
The Integrated Financial Management System (IFMS) is a unified digital platform designed to streamline and modernize public financial management for the Government of Rajasthan. It integrates core functions including budgeting, expenditure control, revenue collection, and accounting to enhance...
Cyber Hygiene at Scale Securing Government LAN and Endpoints using MOGLES & CAAR
To address the complex cybersecurity needs of government infrastructure, a custom framework Model of Government LAN & Endpoint Security (MOGLES) has been formulated and successfully implemented across critical ministries. Complemented by the Continuous and Automated Assessment and Remediation (CAAR)...
Grievance Appellate Committee (GAC) Portal
The Grievance Appellate Committee (GAC), established under the IT Rules, 2021, ensures a Safe, Trusted, and Accountable Internet for Indian users. It provides an online dispute resolution platform for Digital Nagriks (Citizens of India) aggrieved by decisions of Grievance Officers on Social Media...
eChallan
The eChallan system, implemented across all 38 police districts of Gujarat under the One Nation One Challan initiative by MoRTH, is a comprehensive digital platform for traffic enforcement. Integrated with VAHAN, SARATHI, and Intelligent Traffic Management Systems, it enables real-time detection of...




 Subscribe
Subscribe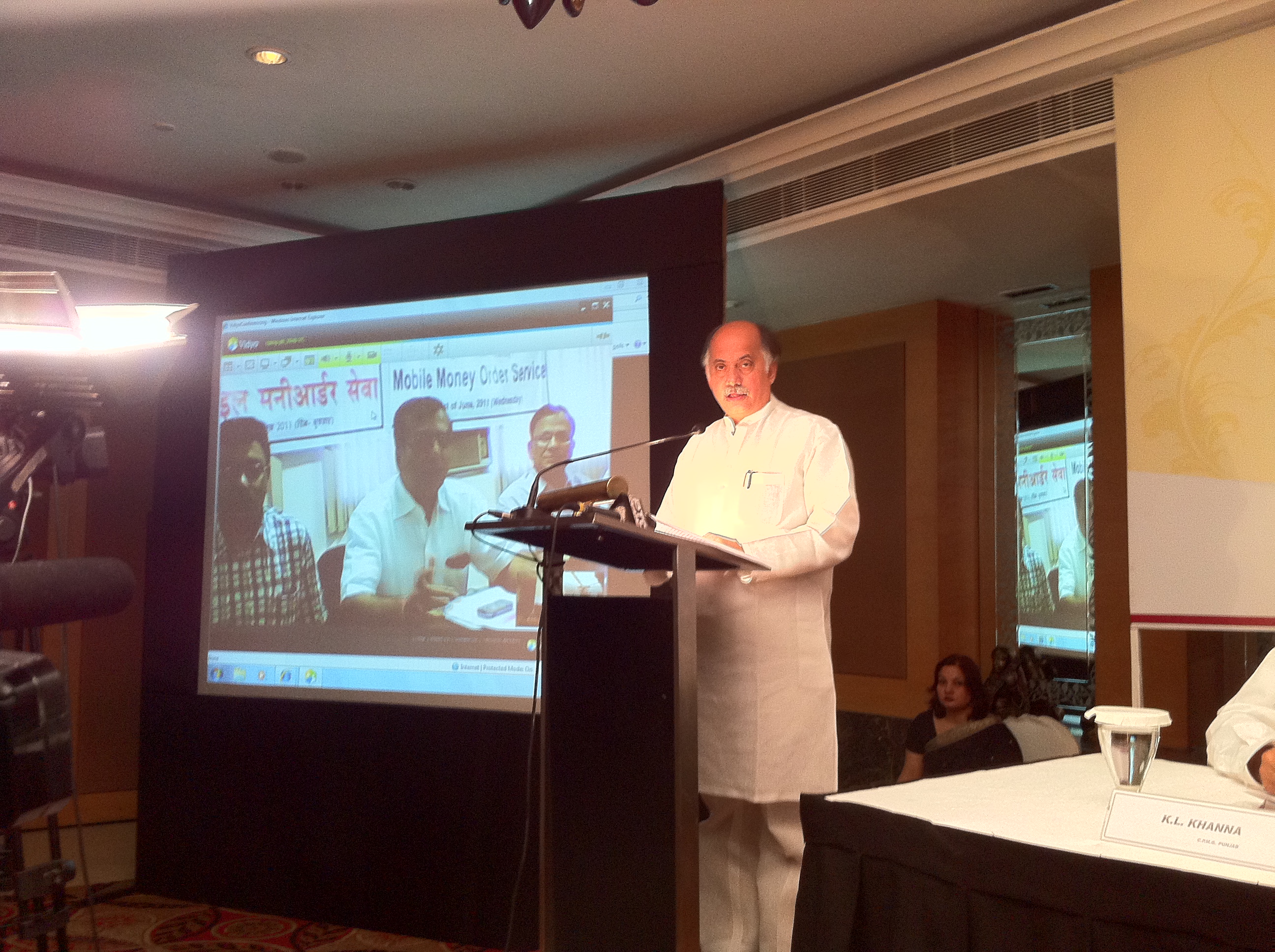





 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


