Technology
Endpoint: The Start Point of Cyber Security - Enhancing Cyber Security through advanced Endpoint Security
Organizations of all types and sizes such as healthcare, finance and defense are at risk from increased volume of organized cybercrime. Being the interface where human beings who are the weakest link in Cyber Security normally interact, these devices are the main targets of malicious actors. Endpoint...
Preventing Cyber Crisis - Must haves for all organizations to secure against cyber crisis
A secure cyber space is crucial for development of any country in economic, political and social spheres. Increased adoption of digital technologies has redefined the cyber security landscape. Cyber crisis is no more a luxury that any progressive state can afford. A set of baseline requirements...
DevSecOps - Producing high quality, secure software at pace
Enterprises across the world are demanding software release at high speed to meet business requirements. when software is developed at such speed, security should not be left behind which can only happen if security is built in to SDLC. Such requirements gave birth to technologies like Agile...
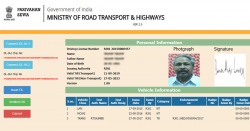
Online Key Management System - for Driving License and Vehicle Registration
A web-based KMS system was considered prudent to be developed for the implementation of specifications notified by the Transport ministry as per gazette notification of 1st March 2019 for Smart card based DL and RC. The new webbased KMS system is designed, developed, and implemented by...
Shimla District - The Queen of Hills Going Digital
District Shimla has tough terrain and most of the area is snowbound, the automation and computerization activities are tough to implement in farflung areas of the District. The citizen service centres named SUGAM have been set up in the lower offices up to Sub Divison and Tehsils. One...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


