Launch
Digidhan Dashboard - Dashboard for monitoring Digital Payments
Digidhan Dashboard enables accurate reporting, monitoring, and analysis of various modes of digital payments and transactions across the country. It provides a consolidated view of 16 digital payment modes such as Unified Payment Interface (UPI), Immediate Payment Service (IMPS), Debit...
e-Labharthi - Heralding a new approach towards electronic service delivery with a Common Social Registry of Beneficiaries for DBT
Students, farmers, pensioners, disabled, poor, and vulnerable sections of the society comprising the bulk beneficiaries of the various schemes of the government of Bihar had a pleasant surprise when they swiftly and securely received their share of fund benefit directly into their bank...
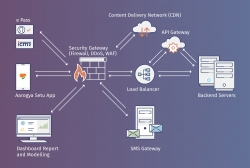
Aarogya Setu App
Aarogya Setu is a mobile application launched by the Government of India on 2nd April 2020, to aid the COVID-19 containment efforts of the Government. The App works based on contact tracing method and helps in identifying, monitoring and mitigating the spread of COVID-19 across the country
Lifeline UDAN Portal - Ensuring steady supply of essentials through airways
All domestic and international flight operations were suspended by the union government with the implementation of lockdown on 25th March 2020 to contain the spread of Coronavirus in the country. However, the transportation of medical supplies and essentials goods needs to be ensured to even a...
RT-PCR App - Mobile Application for Containment and Monitoring Covid-19 pandemic across the Country.
Covid-19 pandemic in India is part of the worldwide situation of coronavirus disease and a large number of people is likely to be affected by the coronavirus. The country has imposed initial lock-downs, supplemented by increased testing of people and contact tracing of patients as effective measures...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


