Cyber Governance
Gujarat Pollution Control Board (GPCB)
The Gujarat Pollution Control Board (GPCB) is a premier body constituted by Government of Gujarat with a view to protect the environment, prevent and control the pollution of air and water in the state. The board has been entrusted with the Central Acts and relevant rules for pollution control as...
News on AIR
All India Radio (AIR) is among the premier broadcasting organizations in the world. The News Services Division (NSD) of All India Radio disseminates news and comments to listeners in India and abroad. Started from 27 news bulletins in 1939-40, AIR today puts more than 651 bulletins...
Workshop on NDSAP and Open Government Platform at Shimla, Himachal Pradesh
A one-day awareness workshop on National Data Sharing and Accessibility Policy and Open Government Platform was held at Shimla on 21-June-2013 under the Chairpersonship of Sh. P.C. Dhiman IAS, Principal Secretary (Information Technology) to the Government of Himachal Pradesh. About 80 officers from...
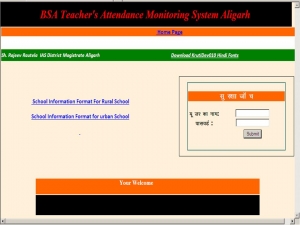
Online System for monitoring Primary Schools in Aligarh, Uttar Pradesh
An online system has been designed and developed by NIC, Aligarh to monitor the prevailing condition of primary schools in the district. The system keeps record of available staff, attendance of students, mid-day meal, uniform distribution, condition of toilets, hygiene, boundary wall, electrical...
Video Conferencing based monitoring of schools and hospitals in Hardoi, Uttar Pradesh.
Days have gone when investigating officers had to plan their visit to the primary schools and government hospitals in the remotest areas of the district to monitor their condition and facilities provided by them. There were many pitfalls in the process; the government school and hospital authorities...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


