Telecom Regulatory Authority of India (TRAI)
The Telecom Regulatory Authority of India (TRAI) was established by an Act of Parliament, called the Telecom Regulatory Authority of India Act, 1997, to regulate telecom services, including fixation/revision of tariffs for telecom services which were earlier vested in the Central Government. The mission of the authority is to create and nurture conditions for growth of telecommunications in the country by providing a fair and transparent policy environment which promotes a level playing field and facilitates fair competition.
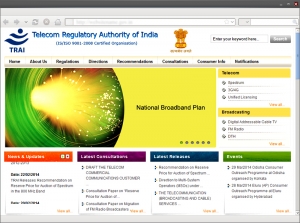
The visually appealing website of the authority deploys judicious use of colours that are sober in nature. The website is rich in content, which is well laid and regularly updated. The header region contains information on the history, structure, organization of TRAI, various regulations, directions, recommendations, consultations, notifications and information for the consumers. This region also displays various images transitioned with the help of an image slider. The content boxes placed below the image furnish information on News & Updates, latest consultations and releases. The footer region highlights information on RTI, related links, Website Policies, Archives, Disclaimer etc. The use of navigation menus, elaborated Sitemap and Search button assists in quick and easy navigation between pages.
The website provides Screen Reader Access and is available in Hindi and English languages. In terms of interactivity, the users can provide their feedback and suggestions in the boxes provided inside the Feedback section. The site is compatible with all major browsers but can be viewed at screen resolution of1024 X 768.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


