ICT for Women Welfare and Child Development, Uttar Pradesh

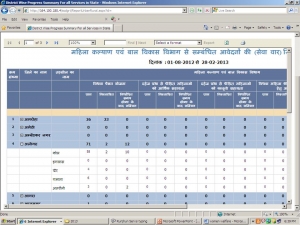
Gone are the days when poor rural women had to run around various government offices and travel across long distances to submit an application for government scheme/service or get a caste, income or domicile certificate. Government of Uttar Pradesh has implemented the eForms application for 26 government services of 8 line departments. Any citizen can apply for these services by visiting a government authorised kiosk near his/her residence. Women welfare and child development department is one of the eight departments whose five services have been offered through the new system. The services include - application for pension to widows, application for financial assistance to woman of dowry scheme, application for legal assistance to dowry sufferers, application for grant for marriage of daughter of widow destitute and application for dampatti puraskar scheme to promote widow marriage.
In order to avail these services an applicant just needs to visit the nearest kiosk (Common Service Centre or Lokavani Centre) with the filled application form and required attachments for example (an applicant of widow pension scheme needs to submit photocopy of BPL card, income certificate and beneficiary's photographs). A comprehensive list of the required attachment for a service is also provided at the portal (uponline.up.nic.in) for easy reference by the citizens under the section SSDG/eForms. Once the application is presented at the kiosk, the kiosk operator verifies the documents and fills the application electronically at the portal using eForms. As soon as the application is submitted electronically an automated receipt is generated with a unique code known as the ‘Application Reference Number’ for the citizen. This number can be used by the applicant to track the status of her application. The receipt with other information also carries the expected delivery date of the service based on the service levels fixed by the government. All the certificates/letters are delivered to the citizens from the kiosks and are digitally signed by the concerned authority. This new system has not only improved the process workflow, it has also brought the services at the doorstep of the women, especially those living in far flung and remote areas of the state.
Till now more than 1400 applications have already been received through the new system.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


