Govt. of Puducherry Launches Security Guidelines for Government Websites and Cloud Applications

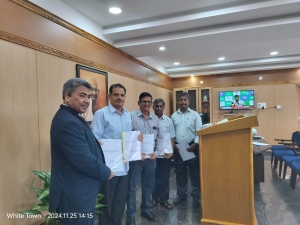
On November 25, 2024, Dr. Sharat Chavhan, I.A.S., Chief Secretary to the Government of Puducherry, released the Security Guidelines and Mitigation Plan for government websites and applications hosted in the cloud environment. This significant step aims to strengthen cybersecurity and ensure the resilience of digital infrastructure in the Union Territory of Puducherry.
The event coincided with the visit of Shri Prashant Kumar Mittal, Deputy Director General and State Coordinator for NIC Puducherry, accompanied by Shri V. Gopiswaminathan, State Informatics Officer, and other NIC officers.
The guidelines provide a comprehensive framework for securing government websites and applications, focusing on mitigating vulnerabilities and ensuring compliance with best practices in cybersecurity. The adoption of these guidelines is expected to enhance the reliability, integrity, and security of cloud-hosted government services, which form the backbone of Puducherry's e-Governance initiatives.
Dr. Chavhan emphasized the critical need for robust security measures in the current digital age, particularly with the increasing reliance on cloud-based technologies. The guidelines will serve as a blueprint for departments to safeguard sensitive data, prevent cyber threats, and build user trust in government digital services.
The collaboration between the Government of Puducherry and NIC Puducherry underscores the commitment to fostering a secure and efficient digital ecosystem, ensuring the seamless delivery of public services while prioritizing cybersecurity.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


