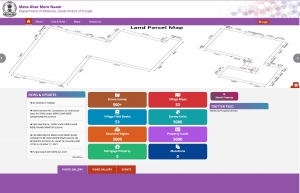
Mera Ghar Mere Naam (MGMN) Portal Department of Revenue, Govt. of Punjab
Revenue Department, Punjab has released an Information, Education and Communication (IEC) booklet for conceptualisation, development and implementation of MGMN scheme in the State by development of state wide portal.
The MGMN portal will cover all the aspects of MGMN implementation covering role of different stakeholders such as Revenue Department, PLRS, Survey of India and NIC etc. The role of NIC Punjab has been given prominent place along with the blueprint of the software solution and technical support of NIC-Punjab on GIS, particularly in the pages 13 to 16.
https://abadirecords.punjab.gov.in/Files/Notifications/IEC BOOKLET PUNJAB.pdf
MGMN is an ambitious scheme of Government of Punjab to accord property rights to lawful owners/occupants with in Lal dora.NIC Punjab has been entrusted as Technology Partner to develop a workflow based software application/portal as per Punjab Abadi deh (Record of Rights) Rules, 2021, to facilitate management and monitoring property ownership to the dwellers living in the houses within Lal Lakir in villages. It will enable them to use their property as a financial asset for taking loans and other financial benefits and will provide the right to make properties marketable and sellable. Using the Web Portal, the owner may search the property and download the property card as well.The software will be developed in phases, initially for creating record of rights, integrating with survey unit maps. Later a provision will be made for property mortgage, sale deeds and updating mutations. Integration with GIS Portal and DigiLocker has been envisaged in later stages.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


